Two-Factor Authentication
You have analytics data you don’t want anyone else accessing. A stolen password alone should never be enough to break in. HitKeep supports two second-factor methods: TOTP (time-based one-time passwords, compatible with any authenticator app) and Passkeys (WebAuthn, compatible with hardware security keys, Face ID, Touch ID, and Windows Hello).
TOTP (Authenticator App)
Section titled “TOTP (Authenticator App)”TOTP is compatible with Google Authenticator, Aegis, Bitwarden Authenticator, 1Password, and any RFC 6238-compliant app.
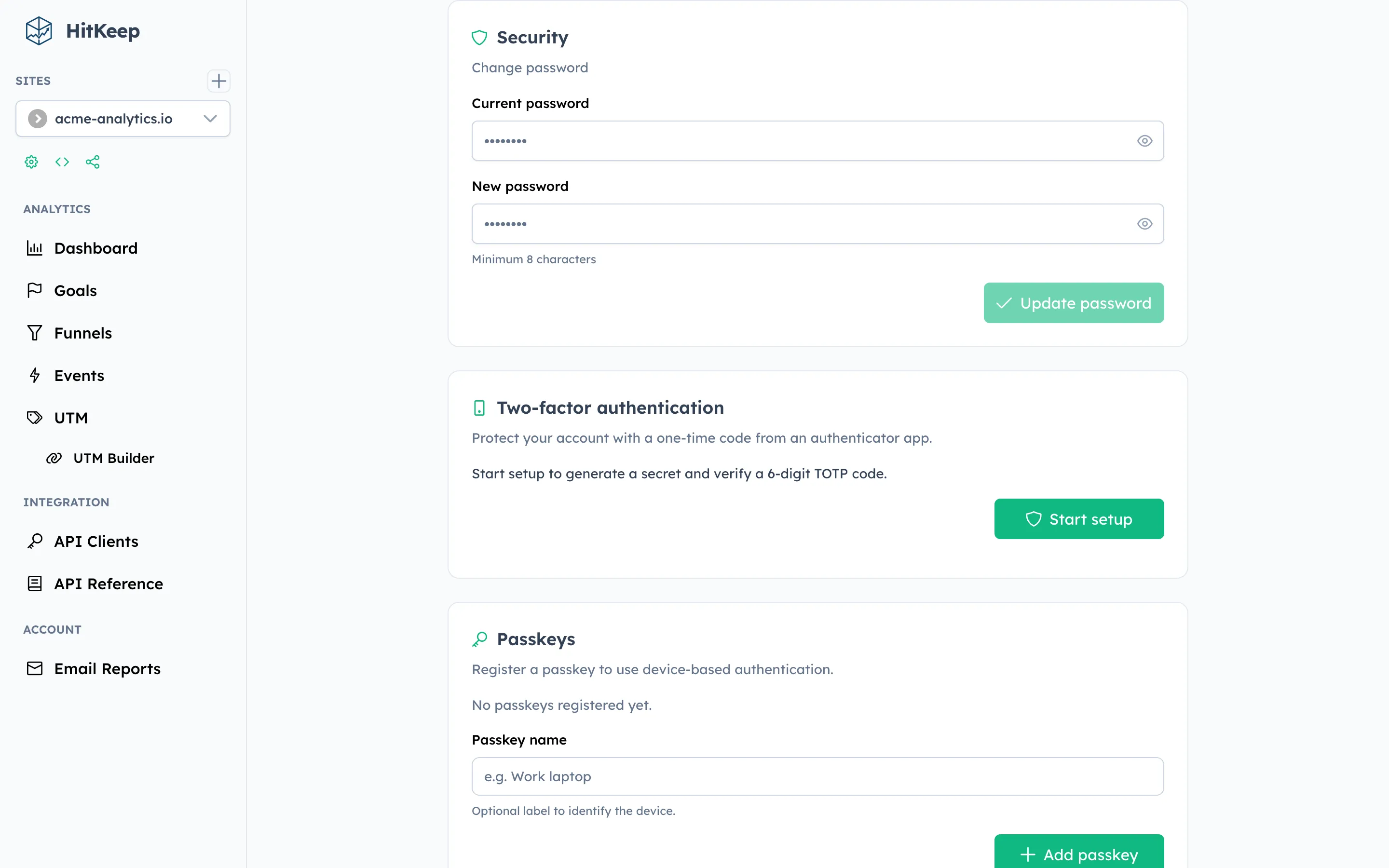
- Open Settings → Security in the HitKeep dashboard.
- Under Two-Factor Authentication, click Set up authenticator app.
- Scan the QR code with your authenticator app.
- Enter the 6-digit code displayed in your app to confirm.
TOTP is now active. On future logins you will be prompted for the current code after entering your password.
# Step 1: Start TOTP setup (returns a provisioning URI / QR code data)curl -X POST https://your-hitkeep.example/api/user/security/totp/setup/start \ -b "hk_token=YOUR_SESSION_COOKIE"
# Step 2: Verify and activate with the 6-digit code from your appcurl -X POST https://your-hitkeep.example/api/user/security/totp/setup/verify \ -H "Content-Type: application/json" \ -b "hk_token=YOUR_SESSION_COOKIE" \ -d '{"code":"123456"}'Disable TOTP
Section titled “Disable TOTP”curl -X POST https://your-hitkeep.example/api/user/security/totp/disable \ -H "Content-Type: application/json" \ -b "hk_token=YOUR_SESSION_COOKIE" \ -d '{"code":"123456"}'Passkeys (WebAuthn)
Section titled “Passkeys (WebAuthn)”Passkeys replace your password entirely with a cryptographic credential stored on your device. Supported authenticators include:
- Hardware keys: YubiKey 5, FIDO2 USB keys
- Platform authenticators: Apple Face ID / Touch ID, Android biometrics, Windows Hello
- Open Settings → Security in the HitKeep dashboard.
- Under Passkeys, click Add passkey.
- Follow your browser’s prompt to register your authenticator.
Once registered, you can log in by clicking Sign in with a passkey on the login page — no password needed.
# Step 1: Get a WebAuthn challengecurl -X POST https://your-hitkeep.example/api/user/security/passkeys/register/start \ -b "hk_token=YOUR_SESSION_COOKIE"
# Step 2: Submit the signed challenge from your authenticatorcurl -X POST https://your-hitkeep.example/api/user/security/passkeys/register/finish \ -H "Content-Type: application/json" \ -b "hk_token=YOUR_SESSION_COOKIE" \ -d '<SIGNED_CREDENTIAL_JSON>'
# Remove a registered passkeycurl -X DELETE https://your-hitkeep.example/api/user/security/passkeys/{passkey_id} \ -b "hk_token=YOUR_SESSION_COOKIE"Passkey Login
Section titled “Passkey Login”# Step 1: Get login challenge (no session cookie required)curl -X POST https://your-hitkeep.example/api/auth/passkey/login/start
# Step 2: Submit signed assertioncurl -X POST https://your-hitkeep.example/api/auth/passkey/login/finish \ -H "Content-Type: application/json" \ -d '<SIGNED_ASSERTION_JSON>'Emergency Recovery
Section titled “Emergency Recovery”If you lose access to your second factor, an instance administrator can run the recovery command directly on the server:
hitkeep recover disable-2fa --email user@example.comSee the Recovery Guide for full details.
Related
Section titled “Related”Prefer not to manage authentication infrastructure yourself? HitKeep Cloud → handles backups, security updates, and account recovery automatically.